|
|
I am working through the System Preferences in OS X. I am now at the letter S, which means Security, Sharing, Software Update, Sound, Speech, Spotlight and Startup Disk. For now, I will skip Q for Quick Time and will add this later. Security is a high priority for all users. While Mac users claim that OS X is more secure than alternative operating systems, there is no reason for complacency. The Security Preferences section is there to be used. It works with other parts of System Preferences (like Accounts and Sharing) for a safer environment if used properly. The Security Preference pane has three sections: General, File Vault, and Firewall.
The second checkbox prevents automatic login. Used with the screensaver lock, Firmware Password Utility and tracking software, this may help us recover a stolen computer. OS X allows a multi-user environment, although some prefer a single user account. A check box locking each preference pane will prevent other users changing the OS settings. If essential tasks are not running, activating the next check box will automatically log the user out after a certain time. The time can be selected in a small panel. The default is 60 minutes. Secure virtual memory is used to ensure that any data, such as passwords, in virtual memory is erased. Finally, in this panel, is a box to disable the infrared receiver used by the remote control. This prevents others using another remote control and accessing media (music, photos, movies). For additional security, the remote device itself can be paired with the computer, also ensuring that others do not have access.
There are two parts to this feature: the file vault protection itself, which needs a considerable amount of hard disk space for the file swapping that will occur; and the Master Password. Apple calls this a "safety net" as it will allow unlocking of any File Vault account. If this master pasword is lost, then you can kiss goodbye to your data: not even Apple can help. An extended discussion of File vault by F. J. de Kermadec can be found at the O'Reilly, MacDev Center.
The first is too open for proper security. The second is too harsh limiting operations to only a small list of allowed connections. Updating from 10.4 will default to this setting. The third option is right for most users although may need a little fine-tuning to optimise operations. As new applications are installed, they will access the internet and many will need incoming connections to be allowed. Examples are Safari and Firefox. It is safe to block some applications. I prevent Skype from making incoming connections but I am still able to call out. It is easy to change this if required with a click in the panel that lists the applications and their status. We can also add an application if it does not make an automatic request. For outgoing connections, a 3rd party utility like Little Snitch is essential.
The other check box in the Advanced panel allows activation of Stealth mode, so that any outside probing that occurs (such as that shown in the logs) will have no response: the computer will not even appear to exist. Anyone who ignores security is taking a gamble.
|
|

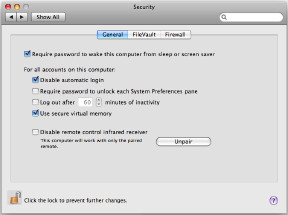 In the General panel is a check box for a password if the computer is in sleep mode or the screensaver active. This is a simple and effective first line of defence. I use this in conjunction with Active Screen Corners: moving the cursor to (in my case) the bottom right of the screen turns on the screensaver and the computer is safe from prying eyes. The only way to circumvent this (if, for example, the computer is stolen) is to restart the computer.
In the General panel is a check box for a password if the computer is in sleep mode or the screensaver active. This is a simple and effective first line of defence. I use this in conjunction with Active Screen Corners: moving the cursor to (in my case) the bottom right of the screen turns on the screensaver and the computer is safe from prying eyes. The only way to circumvent this (if, for example, the computer is stolen) is to restart the computer.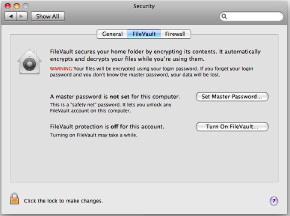 The second panel in Security Preferences focuses on what Apple calls FileVault. The icon (a house with a safe dial superimposed) signifies the ability to lock the users Home folder by way of encryption. If users have this activated, files are decrypted and encrypted while working. A user enters the account as normal, using the password.
The second panel in Security Preferences focuses on what Apple calls FileVault. The icon (a house with a safe dial superimposed) signifies the ability to lock the users Home folder by way of encryption. If users have this activated, files are decrypted and encrypted while working. A user enters the account as normal, using the password.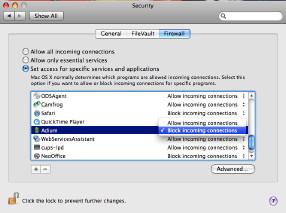 Anyone who does not use a firewall these days is asking for trouble. There were significant changes to the firewall in OS X Leopard. It is now application-focussed rather than port-focussed. It allows a program the correct access instead of specifying port numbers. There are three settings: Allow all incoming connections; Allow only essential services; and Set access.
Anyone who does not use a firewall these days is asking for trouble. There were significant changes to the firewall in OS X Leopard. It is now application-focussed rather than port-focussed. It allows a program the correct access instead of specifying port numbers. There are three settings: Allow all incoming connections; Allow only essential services; and Set access.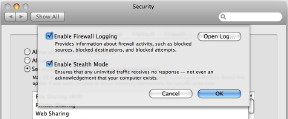 The Firewall panel also has a button marked Advanced. This reveals a further panel with two additional settings. The first enables firewall logging; and the log, if we ever take the time to read it, can reveal some interesting or disturbing information. I see this morning that CAT, a local ISP and my web-host have all probed my Mac. The log may only be accessed by an Admin user.
The Firewall panel also has a button marked Advanced. This reveals a further panel with two additional settings. The first enables firewall logging; and the log, if we ever take the time to read it, can reveal some interesting or disturbing information. I see this morning that CAT, a local ISP and my web-host have all probed my Mac. The log may only be accessed by an Admin user.